Chineses podem ter atacado hardware usado pela Apple e a Amazon nos centros de dados
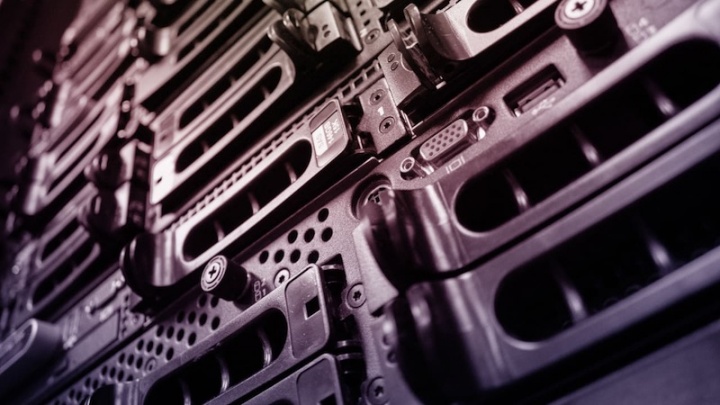
A espionagem industrial tem tomado formas cada vez mais evoluídas e mais originais. O objetivo é claro e pretende apenas o roubo dos dados e de propriedade intelectual. As mais recentes vítimas parecem ter sido a Apple e a Amazon, que viram os seus servidores serem atacados pela China.
Este novo ataque ainda não foi detalhado, mas, segundo a Bloomberg, tanto a Apple como a Amazon viram os seus servidores de dados serem atacados de uma nova forma.
Segundo fontes associadas a este assunto, que se quiseram manter anónimas, terá sido a empresa Super Micro, a fornecer servidores para estas empresas, que foram atacadas. Para além da Apple e da Amazon, cerca de mais 30 empresas foram alvo deste ataque.
A forma usada para roubar os dados, pouco comum face ao que é normal, terá recorrido a chips implantados nestes servidores, que depois eram usados para roubar dados das empresas. Estes dados focavam-se em "propriedade intelectual" e "segredos de negócio".
A Apple já foi confrontada com esta informação, negando de imediato a mesma. A empresa não terá encontrado qualquer chip no seu hardware. No caso da Amazon, a informação que existe também dá conta de não terem sido encontradas quaisquer evidências de alteração do hardware ou presença de chips maliciosos.
Também a Super Micro já negou que tenha introduzido qualquer chips no processo de fabrico dos seus servidores. Até o ministro dos negócios estrangeiros chinês veio já a público e afirmou que o seu país é "um defensor da cibersegurança".
Face a estes factos, fica a dúvida do destino que este caso terá. A Bloomberg garante que as suas fontes são fidedignas e que o caso aconteceu realmente. Por outro lado, temos as partes visadas a negar a sua existência. Provavelmente vão haver mais investigações, até do governo americano, para garantir que esses chips não existem e que, caso tenham existido, a situação está resolvida e saneada.
Este artigo tem mais de um ano




















aguardando as cenas dos próximos capítulos…
Não percam o próximo episódio porque nós também não 🙂
É só carregar no botão Trump
Mesmo sendo verdade, o que nos dias hoje não é imaginação, é claro que estes 2 gigantes nunca iriam por em causa a confiança dos seus clientes, mesmo que isso não os afecte directamente.
Aquilo que eu depreendo é que foi ataque as Clouds, correcto ?
Nope , é mais complexo aquilo que a Bloomberg afirma e que foi formalmente negado.Mas não foi nos servidores iCloud. Foi noutros serviços.
Abc
Não se sabe em que tipo de serviços foi. Apenas que alegadamente tanto a Apple como a Amazon compraram servers que tinham este chip embutido. Para que é que os servidores eram utilizados não se sabe.
Curioso , alguns sites retiraram a historia , em todo o caso fica o que Apple afirmou ,( não encontro o da Amazon )
“The October 8, 2018 issue of Bloomberg Businessweek incorrectly reports that Apple found “malicious chips” in servers on its network in 2015. As Apple has repeatedly explained to Bloomberg reporters and editors over the past 12 months, there is no truth to these claims.
Apple provided Bloomberg Businessweek with the following statement before their story was published:
Over the course of the past year, Bloomberg has contacted us multiple times with claims, sometimes vague and sometimes elaborate, of an alleged security incident at Apple. Each time, we have conducted rigorous internal investigations based on their inquiries and each time we have found absolutely no evidence to support any of them. We have repeatedly and consistently offered factual responses, on the record, refuting virtually every aspect of Bloomberg’s story relating to Apple.
On this we can be very clear: Apple has never found malicious chips, “hardware manipulations” or vulnerabilities purposely planted in any server. Apple never had any contact with the FBI or any other agency about such an incident. We are not aware of any investigation by the FBI, nor are our contacts in law enforcement.
In response to Bloomberg’s latest version of the narrative, we present the following facts: Siri and Topsy never shared servers; Siri has never been deployed on servers sold to us by Super Micro; and Topsy data was limited to approximately 2,000 Super Micro servers, not 7,000. None of those servers have ever been found to hold malicious chips.
As a matter of practice, before servers are put into production at Apple they are inspected for security vulnerabilities and we update all firmware and software with the latest protections. We did not uncover any unusual vulnerabilities in the servers we purchased from Super Micro when we updated the firmware and software according to our standard procedures.
We are deeply disappointed that in their dealings with us, Bloomberg’s reporters have not been open to the possibility that they or their sources might be wrong or misinformed. Our best guess is that they are confusing their story with a previously-reported 2016 incident in which we discovered an infected driver on a single Super Micro server in one of our labs. That one-time event was determined to be accidental and not a targeted attack against Apple.
While there has been no claim that customer data was involved, we take these allegations seriously and we want users to know that we do everything possible to safeguard the personal information they entrust to us. We also want them to know that what Bloomberg is reporting about Apple is inaccurate.
Apple has always believed in being transparent about the ways we handle and protect data. If there were ever such an event as Bloomberg News has claimed, we would be forthcoming about it and we would work closely with law enforcement. Apple engineers conduct regular and rigorous security screenings to ensure that our systems are safe. We know that security is an endless race and that’s why we constantly fortify our systems against increasingly sophisticated hackers and cybercriminals who want to steal our data.
The published Businessweek story also claims that Apple “reported the incident to the FBI but kept details about what it had detected tightly held, even internally.” In November 2017, after we had first been presented with this allegation, we provided the following information to Bloomberg as part of a lengthy and detailed, on-the-record response. It first addresses their reporters’ unsubstantiated claims about a supposed internal investigation:
Despite numerous discussions across multiple teams and organizations, no one at Apple has ever heard of this investigation. Businessweek has refused to provide us with any information to track down the supposed proceedings or findings. Nor have they demonstrated any understanding of the standard procedures which were supposedly circumvented.
No one from Apple ever reached out to the FBI about anything like this, and we have never heard from the FBI about an investigation of this kind — much less tried to restrict it.
In an appearance this morning on Bloomberg Television, reporter Jordan Robertson made further claims about the supposed discovery of malicious chips, saying, “In Apple’s case, our understanding is it was a random spot check of some problematic servers that led to this detection.”
As we have previously informed Bloomberg, this is completely untrue. Apple has never found malicious chips in our servers.
Finally, in response to questions we have received from other news organizations since Businessweek published its story, we are not under any kind of gag order or other confidentiality obligations.”
Já sabemos como é historiacamente a posição da apple relativamente a falhas, sejam elas de que tipo for.
https://www.zerohedge.com/news/2018-10-04/explosive-report-details-chinese-infiltration-apple-amazon-and-cia